The development of the framework presented in here was a collaborative effort between me and several of my Untitled INC fellows. Peter Trapp was heavily involved in all aspects of the creation, including lending his surprising design prowess to it. Prof. Dr. Andranik Tumasjan of the University of Mainz (and formerly Technical University Munich) provided very valuable feedback and ideas, as did Dr. Oliver Krause, Dr. Karl-Michael Henneking and Daniel Pichler.
Blockchain, ICOs and bitcoin’s wild ride have been some of the hottest tech topics in 2017. Yet, while people spent billions of dollars on cryptographic tokens, the understanding of the different token types out there is still limited. Even among regular investors and long-standing members of the blockchain community.
 One reason for it — a quite common one in emerging domains — is the lack of clear, generally agreed upon terminology and definitions. For instance, I regularly come across people who refer to all tokens as “cryptocurrencies”. Which, as we are going to see in a minute, isn’t precise. Which is somewhat problematic because precision in language and terminology is the basis for an informed, nuanced dialogue and good analysis.
One reason for it — a quite common one in emerging domains — is the lack of clear, generally agreed upon terminology and definitions. For instance, I regularly come across people who refer to all tokens as “cryptocurrencies”. Which, as we are going to see in a minute, isn’t precise. Which is somewhat problematic because precision in language and terminology is the basis for an informed, nuanced dialogue and good analysis.
Whether you want to develop a token or evaluate one, it’s critical to understand the nuances of the subject. Moreover, the blockchain community is growing and maturing. As a result, it is increasingly getting in touch with “the real world” (aka people who are new to the subject). Investors, regulators, politicians and decision-makers in businesses are all taking the space increasingly serious. Many are in the process of formulating their positions and strategies for dealing with the subject. Clarity and accessibility of relevant knowledge are key to allowing those actors to make good, informed decisions.
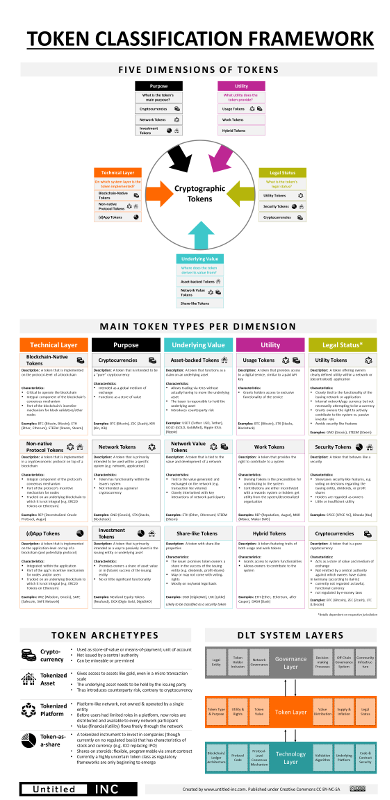
This is why we, the Untitled INC team, set out to develop a framework that a) reflects the various existing token types, b) allows to classify and analyze tokens in various relevant dimensions, and c) fosters a better, nuanced understanding of crypto tokens. Today, we are presenting the first iteration of the Token Classification Framework, the result of our effort. In this post, I’m going to walk you through the framework and explain the work and thinking that went into it.
Introductory Remarks
Before we get into the framework, some technical and procedural remarks.
To develop the framework, we reviewed a lot of work on tokens that had already been put out there. Many smart people published very helpful thoughts and ideas which influenced our thinking and chosen terminology. You’ll find a list of references at the end of this article.
The version of the framework in this article is version 1.0 of the Token Classification Framework (TCF). The crypto space is moving at a rapid pace, so we expect to see new developments and innovative approaches to tokens quite frequently. Thus, we regard the framework as a living document. The version in this article shall serve as a point-of-reference going forward, so we won’t update the TCF in here. Instead, we’ll host and maintain the most current version on our website.
Last but not least, we decided to turn the future development of the framework into a collaborative endeavor. Which is why we are releasing the framework under a Creative Commons BY-NC-SA license. This allows the community to iterate on the framework and contribute to its development. Also, your feedback is highly welcome so please leave your feedback in the comments below.

Classifying Tokens in Five Dimensions
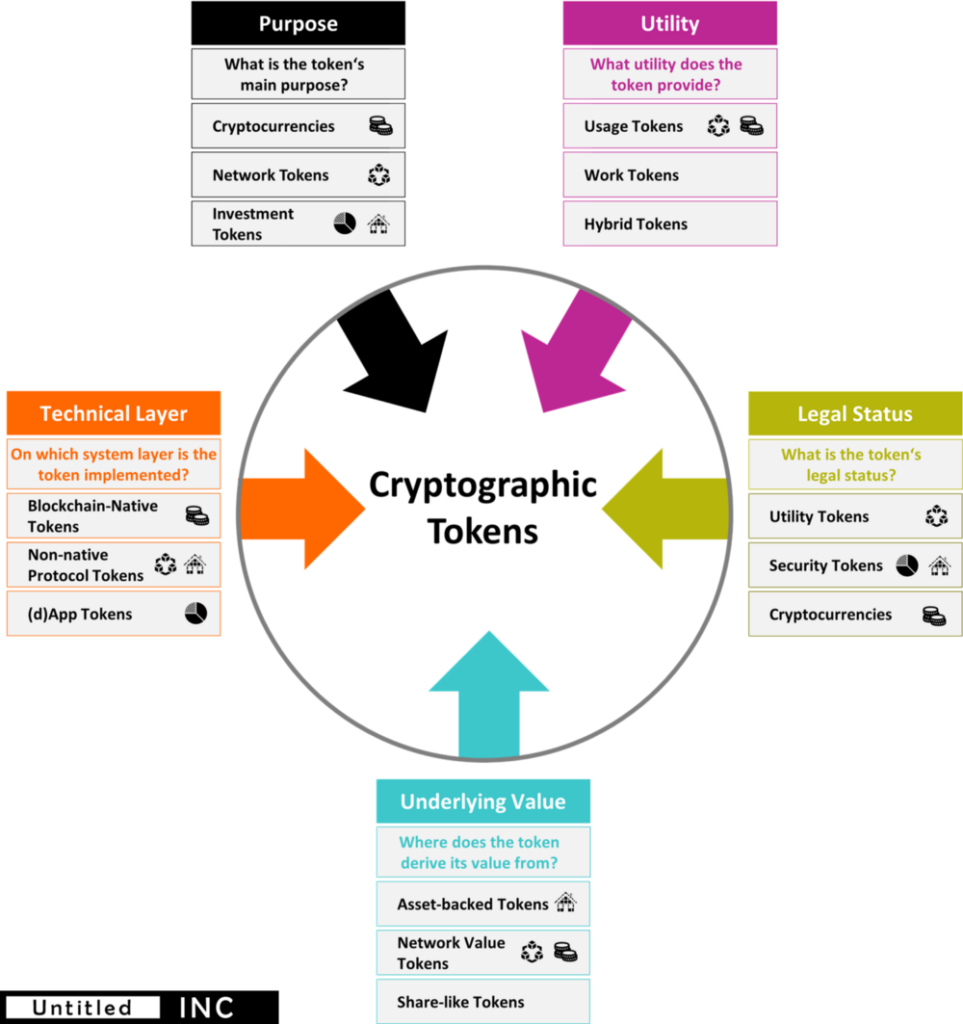
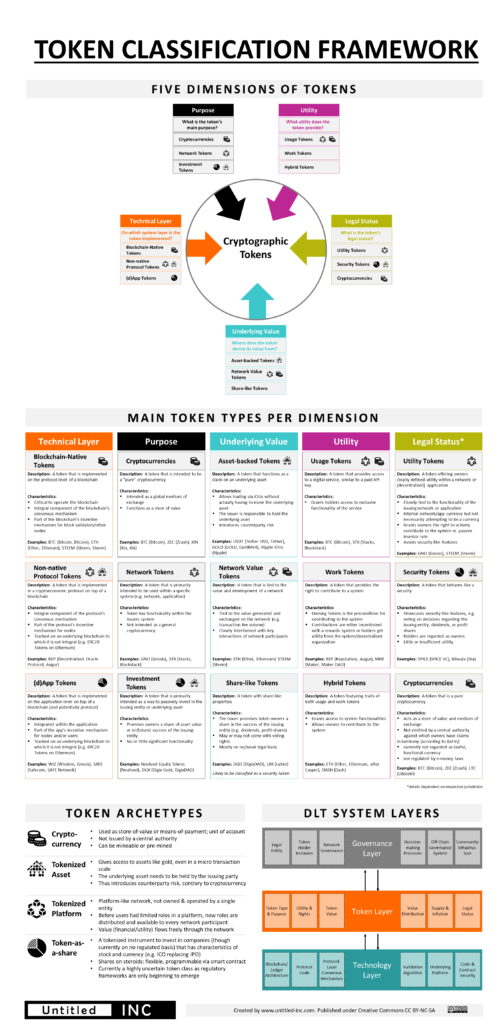
There are multiple angles from which you can look at tokens. Back when we began working on the framework, we quickly realized that it would have to cover multiple perspectives in order for it to be useful. After reviewing the current literature and analyzing dozens of whitepapers, we distilled five major dimensions which we wanted to reflect in the framework: a token’s purpose, utility, legal status, it’s underlying value and the technical layer it’s implemented on.
Purpose. What is the token’s main purpose? What is it designed to do? This dimension illustrates why the people who call any token a cryptocurrency err. Tokens can certainly be intended as a cryptocurrency. But often they are meant to enable a specific network and catalyze its growth (network tokens) or merely present a way to invest in an entity or asset (investment token).
Utility. The term “utility token” has become commonplace¹ but there are various types. When looking at different tokens, you’ll find many approaches to creating utility for token owners. But on an abstract level, there are two major ways to provide utility: by giving access to network or service features (usage tokens) or by allowing token holders to actively contribute work to the system (work tokens). Some tokens do both (hybrid tokens) and some tokens don’t provide any utility at all².
Legal Status. The legal perspective is extremely relevant as of now, so it is reflected in the framework. The category’s content, however, is expected to change quite a bit in the upcoming months as it is a volatile environment and more regulation is expected to emerge. Moreover, every jurisdiction can differ. The general outline of the current state in multiple countries is that tokens which aren’t clearly a utility token — i.e. a means to access features of a network/service — or which aren’t a pure cryptocurrency can easily be classified as a security token by regulators. In some jurisdictions, such as Germany, there is some definition by regulators as to what constitutes a cryptocurrency. Several cases we found hover between two types, due to fact that current legal frameworks have been created before tokens existed and most haven’t been updated so far. (This isn’t legal advice.)
Underlying Value. Most tokens are created to have a monetary value. But the sources of their value differ considerably. Some basically work as IOUs to a real-world asset which they are tied to (asset-backed tokens). Others showcase stock-like properties as they are linked to the commercial success of the issuing entity. Those share-like tokens would be regarded as securities in most jurisdictions (actual enforcement by the regulator is a different subject). Finally, there are tokens which are tied to the value of a network, not a central entity (network value tokens). The latter might be the hardest to wrap one’s head around and the most interesting value source at the same time.
Technical Layer. Tokens can be implemented on different technical layers of blockchain-based systems: on the blockchain level as the chain’s native token (blockchain-native tokens), as part of a cryptoeconomic protocol that sits on top of the blockchain (non-native protocol tokens), or on the application level ((d)App tokens).
It’s important to note that the dimensions are complementary. Most tokens can be assessed in all dimensions and, as we’ll see when looking at the archetypes, there are strong correlations between some types in different categories.

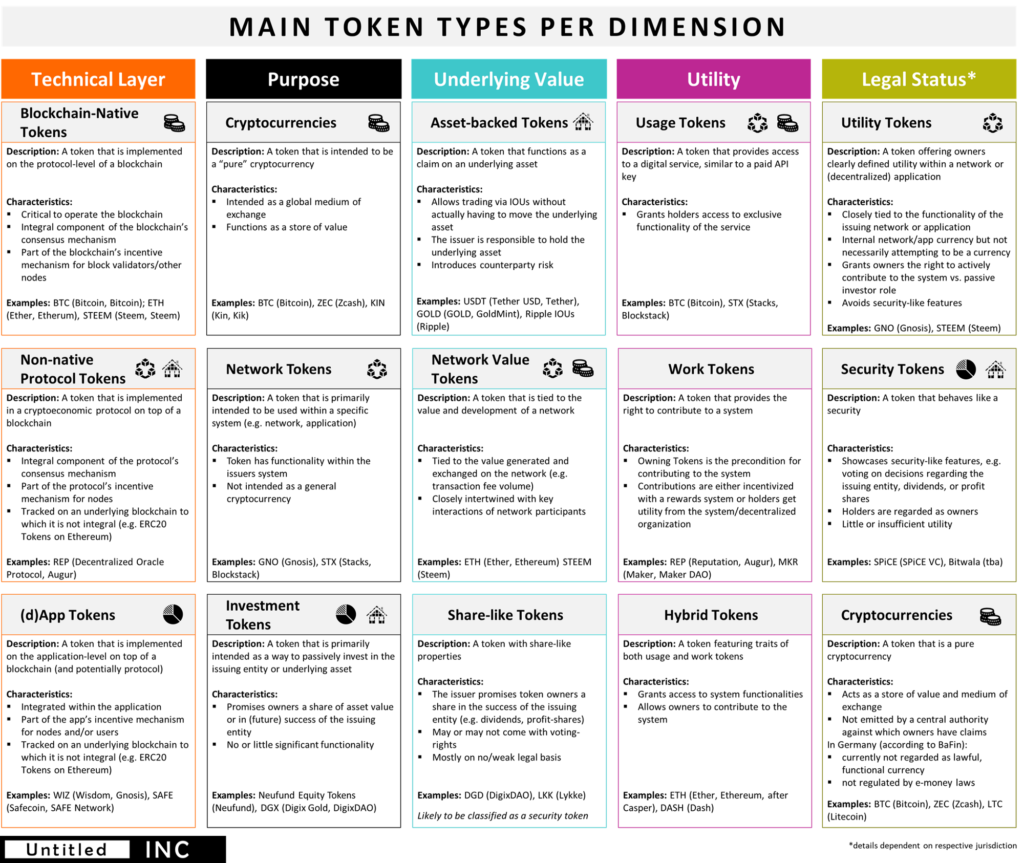
Main Token Types per Dimension
In any dimension, we identified various token types, summarized their main characteristics and included relevant examples. You can find the result in the graphic below.

Putting the TCF to the Test
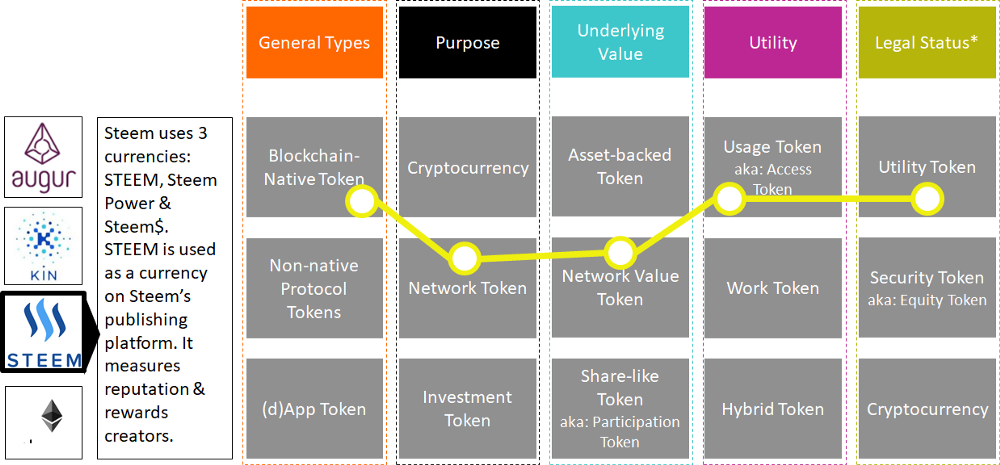
A granular framework like this allows us to understand a given token with a higher degree of precision. In order to put the framework to practice, we looked at several tokens and classified them. You’ll find some examples from a recent workshop we held below:
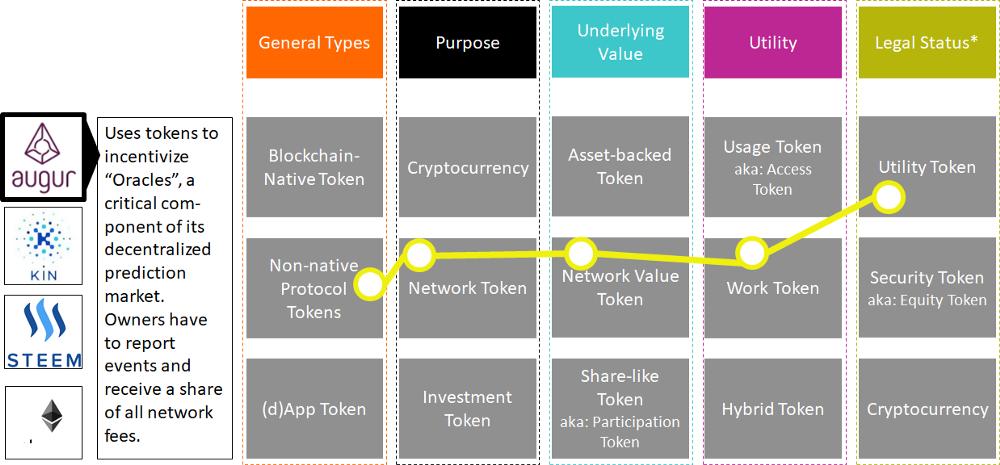
As the first chart shows, you could call Augur’s REP a Non-native-protocol-Network-Network-value-Work token that would likely classify as a utility token.
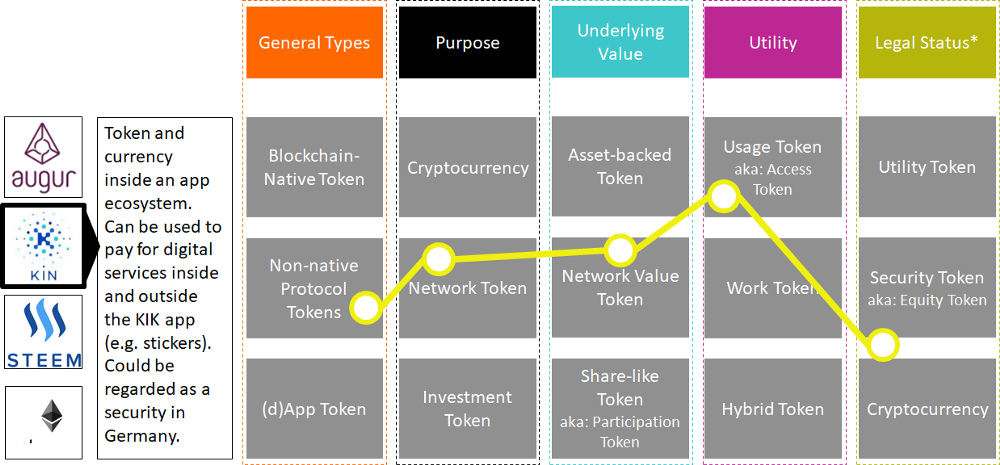
Let’s stop here. If you are interested in playing around with the framework, you might want to start with Ethereum and classify it yourself.

Archetypes
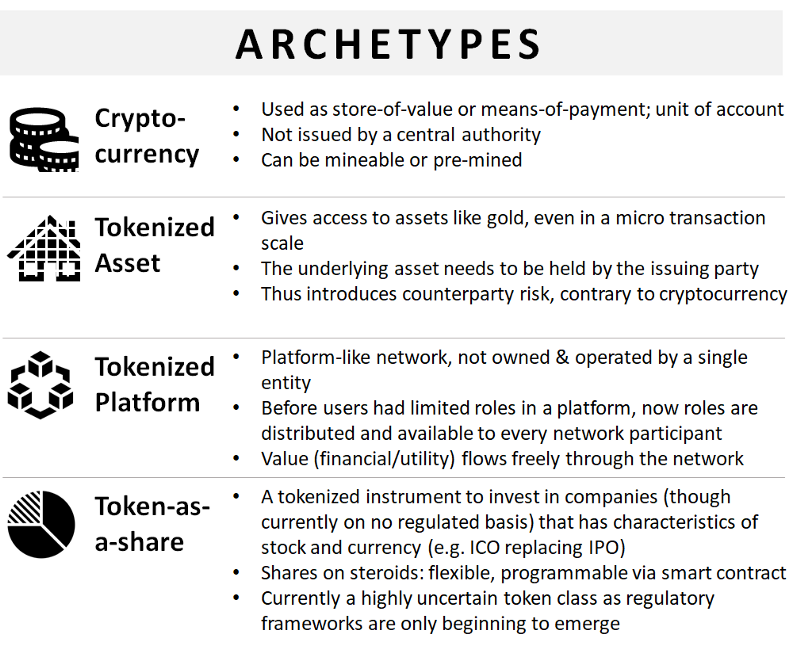
After using the framework to classify a fair number of tokens, some patterns emerged (unsurprisingly). As I said before, there are some rather obvious correlations between different token types. For instance, many network tokens (by purpose) will also be network value tokens, i.e. their value is tied to the value of the network they are used within. Similarly, an investment token will basically never be a network value token but either asset-backed or share-like. We looked at those patterns and derived some archetypes.
Each archetype is represented by an icon. The icons are also included in the main table above, next to the token typology usually associated with a respective archetype. A description of each archetype is included in the graphic below:

The Wider Context
We think the TCF is useful to classify and create more clarity around the various token types you can find today. Still, it is important to note that it isn’t enough to merely analyze a token.
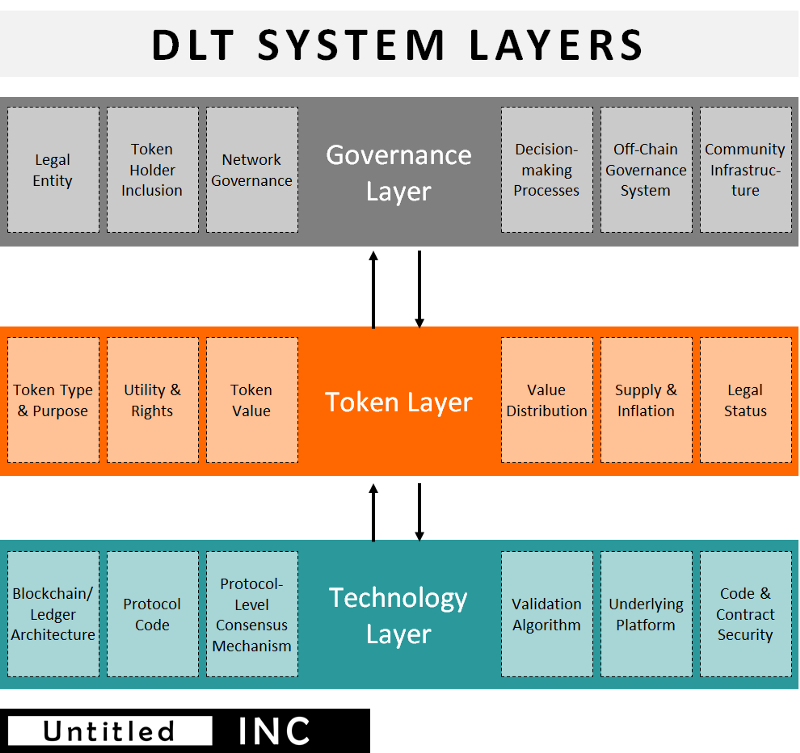
Crypto tokens don’t exist in isolation but are only one component of a distributed ledger system. While tokens are an integral component of the system — as they are critical to establishing a cryptoeconomic dynamic —the token layer is only one of three system layers. The others are the governance and technology layer, which are connected by the token. I won’t go into detail on the model below, as it merits its own post in the future. For now, it’s enough if you keep in mind that any assessment of a DLT project shouldn’t exclusively focus on the token but look at the entire system.

The Complete Token Classification Framework
Now that you are familiar with the different components of the TCF, you can find the complete framework below in high resolution. As it is published under Creative Commons, feel free to share and iterate on it. Just don’t forget to link back to us. And if you have comments or suggestions for further improvements to the framework, please let us know.
> Subscribe to the Untitled INC Newsletter

Final Remarks and Sources
As the blockchain space matures, clarity and a precise terminology become increasingly important. With the TCF, we hope to have created a valuable resource that contributes to a better, more nuanced understanding of tokens. As it is now part of the commons, everybody is invited to further improve it.
What’s not in there
There are two potential dimensions which we thought about but eventually didn’t include in the framework: the Issuance Approach and Supply Structure. In the case of issuance (ICO, airdrop etc.) it’s only a one-off event that we didn’t regard as a fundamental characteristic of the token. It doesn’t influence how the token behaves long-term. Thus, we eventually decided against including it.
In the case of supply (fixed, inflated with cap, inflated without cap), it’s dicier. On the one hand, it is very relevant when it comes to investment decisions. On the other hand, it’s not a characteristic of the token itself but rather a property of the overall system (which is why it’s part if the token layer in the DLT system layers model but not a token dimension). Depending on your feedback, we might rethink our decision, though.
Sources
Bulkin, Aleksandr; Cryptoeconomics Is Hard; CoinFund; 2017; Aleksandr Bulkin
Cicero, Simone; Blockchain Powered Platforms; Stories of Platform Design; 2017; Simone Cicero
Dixon, Chris; Crypto Tokens: A Breakthrough in Open Network Design; Medium; 2017; Chris Dixon
Mougayar, William; Tokenomics — A Business Guide to Token Usage, Utility and Value; Startup Mangement; 2017; William Mougayar
Svrinivasan, Balaji S.; Thoughts on Tokens; earn.com; 2017; Balaji S. Srinivasan
Tomaino, Nick; On Token Value; The Control; 2017; Nick Tomaino
Various; A Securities Law Framework for Blockchain Tokens [PDF]; Coinbase; 2016; Coinbase
¹ Mostly because everybody who performs an ICO emphasizes that the issued token is a utility token in order to avoid being regarded as a security.
² While tokens which don’t provide any utility are often frowned upon, that thinking shouldn’t be generalized. While its often a characteristic of scams, an asset-backed token doesn’t necessarily need any further utility to be legitimate.
Author: Thomas Euler
Thomas is an experienced consultant, analyst, and writer at the intersection of tech, business, and the digital economy. He has been researching and regularly covering the blockchain space for several years now as he has long been interested in decentralized systems and new types of organizations.

What is this reddit thread you speak of?
Hi Marty, thanks for hinting me at this. It was actually a lost sentence. It was an initial idea to collect feedback in a Reddit thread, Eventually, though, we figured that sticking to the comment section might be simpler and clutter things less.
Hi Thomas,
great work. Why don’t you upload it to medium and steem it.
I ve heard about your framework in the Bundesblock Slack group.
Philipp
Hi Philipp,
thanks, glad you found it helpful! It actually already is on Medium. Steemit is a very good idea though (apparently it flies just below my publishing platform radar ^^)! Will put it on there asap. Appreciate the hint 🙂
Can’t read the chart. Too small in the native webpage and when blown up too pixilated. I’d love to share this with my meetups.
Hi Gerry, thanks for the hint! That obviously was a mistake and it should be fixed now. If you click on the big graphic at the article’s end, you get to another page on which you find the proper file.
great work!
Thanks 🙂
This is a great article Thomas, have you considered perhaps this could be a foundation to a terminology standard for blockchain technology? This would be a good submission to the European Commissions exploration into the subject matter as a definition section.
Hi John, thanks for your comment!
I think that a clear and agreed-upon terminology is very important indeed. I would assume that it usually emerges once certain actors, particularly academics, begin to establish an “official” terminology for a new field. Sure enough, the framework here is also intended as a contribution to the development of such terminology.
However, I’m not sure you can effectively “standardize” language – you would also have to drive adoption by the community. Which, of course, doesn’t mean that it wouldn’t be helpful to create a resource which suggests a clear terminology, ideally after developing it together with practitioners from the community. If you have any ideas in those regards, let me know. I definitely think that it would be a worthwhile and useful endeavor!
Awesome job, gave you a shout out: https://www.coinstaker.com/types-of-tokens-the-classification-framework
Looking forward to the governance part.
Hi Philip, great! Thanks a lot for spreading the work!
This will be helpful for non-technical speculators and investors to better understand the projects they’re supporting.
Your contribution will also make it easier to navigate the complexity of the ecosystem.
Thank you.
Thanks for the enlightenment. You just made my job of educating customer much easier.
Very useful! Looking forward to your follow up work.
Dear Thomas and team,
1. This is a wonderful framework. Do continue to improve on it and if possible, provide more examples for the community.
2. To me, the above framework in totality is akin to the Business Model Canvas / Lean Canvas which we use in the entrepreneurship and angel investors communities.
3. Very well done.
One more thing, how would you like us to cite/reference this piece of good work?
Dear Dr. Yeap,
Thanks for asking! Online, simply link to this article and/or the maintenance site and mention Untitled INC (and myself if you need a person as well). In an academic context, the publication should be Untitled INC Blog.
I hope that helps 🙂
Fantastic read, logical and succinct- thanks you Thomas!
Hi Thomas,
I find amazing this TCF. I like the clarity, structure, ideas and chart.
Thank you very much for sharing.
Great job!
Great stuff! Congrats.
A minor thing, though, you should make it clear what “DLT” stands for.
Nice read, Thnx.
Ardor/nxt/ignis fits in all 😊
Great elaboration on the different types of tokens. I was just wondering if the ICO crowdfunding tokens falls into the asset-based or network value type.
Look forward to more of your articles. Thanks.
Hello. Curious, where would you slide BTC in for underlying value?… Do you believe some assets are not going to fit anywhere in this matrix cleanly, as in 1 mark per column? Thanks.
Excellent work Thomas. I believe this is the best token classification approach that I have seen so far. I have some questions/feedback and I will love to hear your thoughts on those:
– In the technical layer, you have not included a class for tokens that are neither protocol level nor DAPP. E.g. an equity token issued as ERC20.
– In “Purpose” you have not placed Ether in any example. Will you place it in cryptocurrency or network token or both?
– On the legal status, what you call utility token appears to be a “Network Fee” i.e. the token will be used to pay the fee for the future utility of the network and will be then burned. I think it would be great to have unique name for each type in different layers, i.e. 15 unique names for clarity. Is it too much to ask?
– I noticed that you have not included the supply intentionally and I agree with your argument some extent though I would have used the following types; 1) Fixed (bitcoin) 2) Inflating/Incremental (Ether) 3) Depleting (Ripple)
I am planning to develop a valuation model leverage this work and I will include “supply management” as a variable there.
Thomas, A great work! Just wonder how do you classify ETH? It seems that it’s not viewed as a cryptocurrency in your TCF? Am I missing anything? Thanks.
@Rui DLT stands for “Distributed Ledger Technology”
Thomas,
I have been learning and doing intensive research over the last 10 weeks, putting together a business plan with the goal of launching an ICO. This article is one of the finest ones I have found so far. Congratulations and hope we can get in touch some time in the near future.
Humberto
Super …. will be of great support in the legislative project I am leading in Malta where we are currently grappling with the issue of how and at what level to deal with tokens. the focus of our project is the legal entity which will be issuing the tokens and the effects of tokens vis a vis the entity (security, debt or derivative), vis a vis functionaries (core developers, administrators, miners, oracles, forensic nodes), vis a vis third parties (attachment, pledges, transfers and liability), vis a vis regulators and courts (their powers) on a classification intimately connected to or based on the type of DLT platform (centralised, decentralised or hybrid) and the different purposes which could feature (private/ commercial or non-profit/public benefit purposes). The angles of sight and perspective are endless and that may need a high level principle based approach to avoid detail in law which will quickly go out of relevance with the fast pace of change.
Thanks for Sharing such a piece of great information.